Networking
Modern technology is incomplete without networking. Networks are the support of the internet since they connect devices to the management of the data. In the case of Class 9 students, they should know how networks operate and what tools are used to assist them, as well as how they can ensure the safety of data in the networks using network security.
This article will discuss the fundamentals of networking, such as the key concepts of networking (the OSI model and TCP/IP model), data security, and the practice of ethical hacking and cloud networking in the modern world of the Internet.
What is Networking?
Networking can be defined as the process of linking computers and other devices so as to exchange data and resources and communicate with one another.
Networking enables the sharing of information among devices such as computers, printers, smartphones, and servers.
Key Networking Concepts:
- Network Devices: Hardware equipment such as a router, a switch and a modem that facilitates connection and communication between devices.
- Data Transmission: Data that is passed on through the network amongst devices in a network that is commonly divided into small data packets.
- Protocols: Rules that specify the communication way of the devices in a network.
OSI Model: Data Layer Information
The OSI model (Open Systems Interconnection) describes the flow of data within a network in 7 layers. All layers serve a purpose in order to ensure that communication is efficient and reliable.
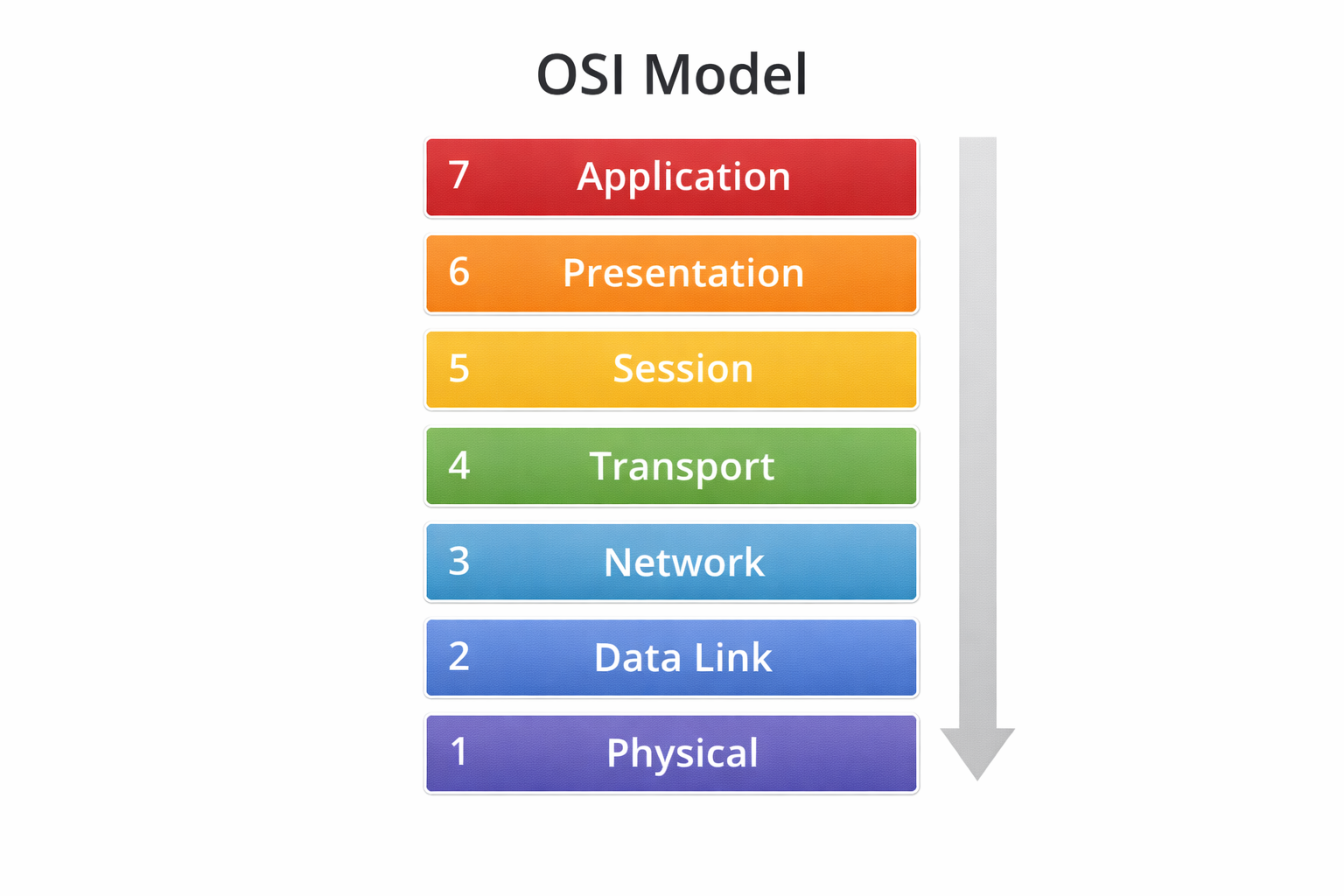
7 Layers of OSI:
- Physical Layer: The physical layer is concerned with data transmission and hardware.
- Data Link Layer: Provides reliability in the transfer of data among other devices in the same network.
- Network Layer: Data routing and addressing (such as IP addresses).
- Transport Layer: Makes sure that data is transmitted correctly and with efficiency.
- Session Layer: The session layer is in charge of sessions or connections among devices.
- Presentation Layer: Converts data to a readable one to use in the application.
- Application Layer: This is a layer that interacts with the user, such as email or web browsing.
Why Is It Important?
- The OSI model aids in structuring and simplifying network communication.
- It enables network troubleshooting on different levels.
- It assists in standardising the communication between devices and thus becomes interoperable.
TCP/IP Model: The Internet Backbone
The TCP/IP model is a more basic model of four layers that is applied in communicating data over the internet.
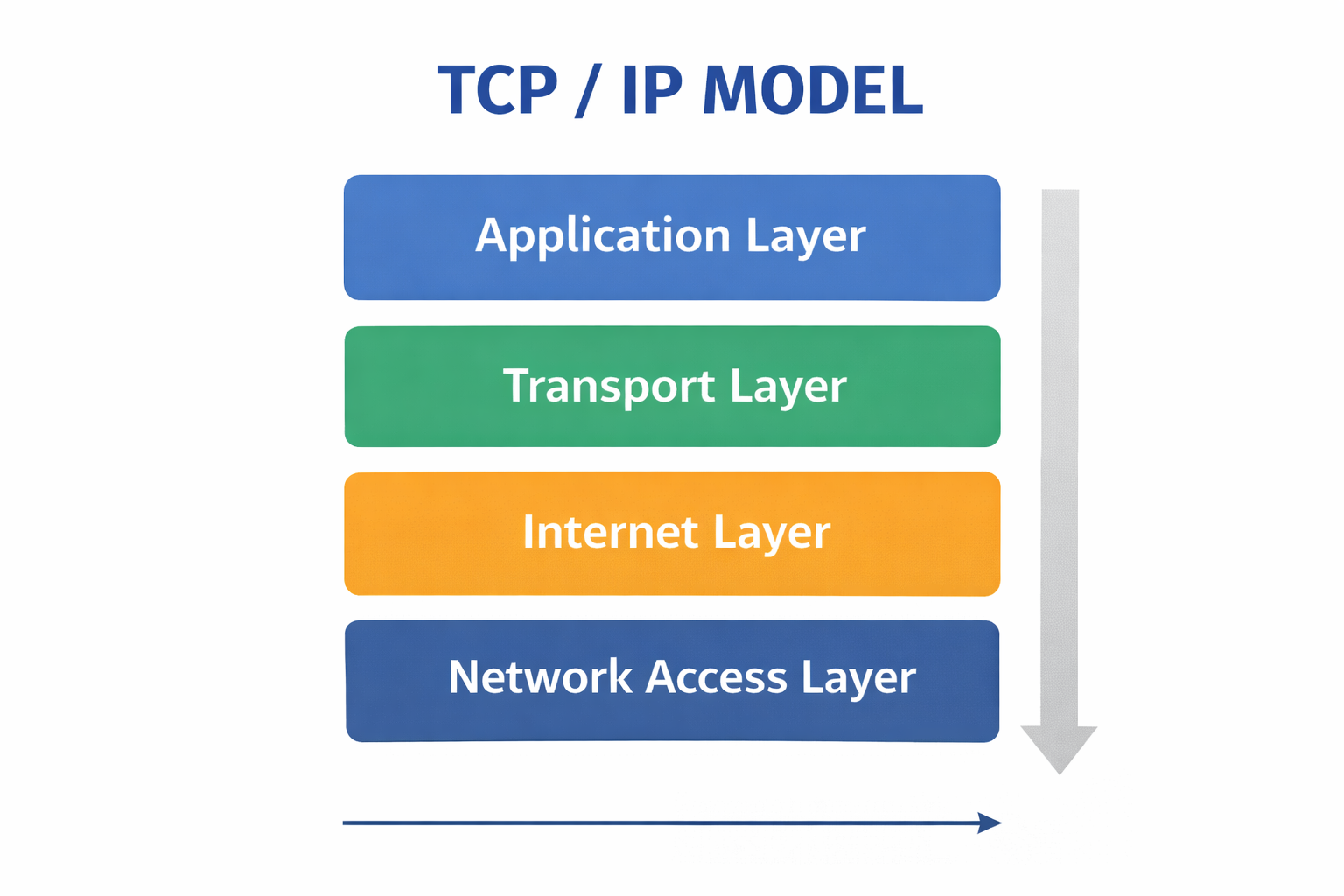
4 Layers of TCP/IP:
- Application Layer: Processes applications such as web browsing, email, etc.
- Transport Layer: controls data transfer between ends (data delivery is correct).
- Internet Layer: addresses the data routing and IP addresses.
- Network Access Layer: It controls the physical transmission of data on the network.
Why Is It Important?
- It is the platform of internet communication.
- It aids internet-based devices in communication by providing a stable means of transfer of data.
Network Security Measures
With the internet playing an important role in the lives of the common people, the security of networks is a very important issue. The security systems apply to the data to prevent theft and manipulation by hackers.
Common Security Measures:
- Firewalls: Secure networks by blocking unauthorised access by monitoring the incoming and outgoing traffic.
- Antivirus Software: Scans and gets rid of bad programs (malware).
- Good Password Policies: The use of complex passwords so that hackers find it hard to decode them.
- Two-Factor Authentication (2FA): This increases the level of security by a second verification procedure.
- Regular System Updates: Makes devices secure through vulnerability fixing.
Why Is It Important?
- Network security assists in securing important data against cyberattacks and unauthorised access.
- It provides security in data integrity and protects your devices against malware.
Data Privacy and Protection
Data privacy can be defined as the security of personal data that is stored on the digital platforms. In the modern world, where personal data is frequently provided by the Internet, one should be sure that his or her information is safe.
How to Protect Your Data:
- Use a strong password: use letters, numbers and symbols when creating passwords.
- Two-Factor Authentication (2FA): Provides added security to make your accounts more secure.
- Understand Your Digital Footprint: Pay attention to what you post on the internet. All your activities on the internet create an impression.
Why Is It Important?
- Data privacy will ensure that your personal information is not abused.
- It is also confidential, and it prevents identity theft or financial fraud.
Introduction to Ethical Hacking
Ethical hacking is a system that is tested internally with the aim of establishing its vulnerability. White hat hackers are contracted to assist in enhancing network security and defending against cyberattacks.

The main features of ethical hacking:
- Permission-Based: White hat hackers are always granted access to test systems.
- Enhances Security: They detect vulnerabilities within systems and attempt to seal them before evil hackers can take advantage of them.
- Secures Organisations: Ethical hackers assist companies in protecting their networks and information.
Why Is It Important?
- Cyberattacks and confidential information should be avoided, and this is possible through ethical hacking.
- It assists companies and organisations to remain secure and enhance their security infrastructure.
Basics of Cloud Networking
Cloud networking enables organisations and individuals to save and control data via the web instead of using hardware.
The advantages of cloud networking are the following:
- Anywhere Access: Data can be accessed anywhere using any device that has an internet connection.
- Automatic Backup: Data is automatically backed up in the cloud, which lowers the chances of loss of data.
- Improved Data Management: Cloud computing provides the means for more convenient data management and handling.
Why Is It Important?
It makes sure data is easily accessible, secure and manageable.
QUIZ FOR NETWORKING
1. 'Networking' mainly refers to:
A) Installation of operating systems.
B)Linking devices to exchange data and resources.
C) Computer hardware design.
D) Programming applications
Answer: B) Linking devices to exchange data and resources.
2. What is the hardware device that links multiple networks and routes the data packets?
A) Printer
B) Router
C) Scanner
D) Monitor
Answer: B) Router
3. In networking, information is normally passed in small sized units known as:
A) Blocks
B) Frames
C) Packets
D) Bytes
Answer: C) Packets
4. Which layer in the OSI model is in charge of routing data based on their IP addresses?
A) Physical Layer
B) Network Layer
C) Transport Layer
D) Presentation Layer
Answer: B) Network Layer
5. What OSI layer translates data into something that the application can comprehend?
A) Session Layer
B) Presentation Layer
C) Data Link Layer
D) Application Layer
Answer: B) Presentation Layer
6. How many layers are in the TCP/IP model that is popular on the internet?
A) 3
B) 4
C) 5
D) 7
Answer: B) 4
7. What TCP/IP layer performs network IP addressing and routing of data?
A) Application Layer
B) Transport Layer
C) Internet Layer
D) Network Access Layer
Answer: C) Internet Layer
8. What is the network security tool that will check and prevent unapproved network traffic?
A) Antivirus
B) Firewall
C) Router
D) Switch
Answer: B) Firewall
9. Permission call testing systems to determine security weaknesses is known as:
A) Data mining
B) Ethical hacking
C) Cloud computing
D) Packet switching
Answer: B) Ethical hacking
10. Storing and handling data on the remote servers, which are accessed via the internet, is referred to as:
A) Network switching
B) Cloud networking
C) Data routing
D) Packet filtering
Answer: B) Cloud networking